Tax Time is Scam Time
It’s that time again. April 18 is fast approaching and tax returns will soon be due. (The filing deadline this year is April 18 instead of April 15, due to Emancipation Day.)
Whether you do your own taxes or have someone else prepare them, your taxes are probably on your mind, or will be soon. But you’re not the only one thinking about this. Someone else is, too, but they are thinking about it from a different perspective. This is a time of opportunity! An opportunity to take advantage of you and use it to get your sensitive information and maybe your money as well. Continue reading “Tax Time is Scam Time”
The Security Soluton – Part 4
Today, we conclude the discussion of a “four-step solution” to security problems. Once you have taken reasonable measures to keep bad things from happening and accepted that they will sometimes still occur, you can move onto the next step. You can take measures to limit the negative consequences if they do occur. Continue reading “The Security Soluton – Part 4”
(A Critical Part of) The Solution – Part 3
Today I want to provide a very important part of the solution to security problems: Realize that bad things will still occur despite all efforts to prevent them.
That may sound strange. How can it be a solution to say that we can’t come up with a solution that will keep bad things from happening? I will get to that in a moment.
But first, I want address the idea that we can stop bad things from happening.
We buy antivirus software in the hope that it will keep us free from viruses. It won’t. It will detect and stop a lot of viruses. But it won’t catch them all. Sorry about that. Continue reading “(A Critical Part of) The Solution – Part 3”
The Security Solution – Part 2
Last week, I talked about taking appropriate measures to make it harder for bad things to occur.
This week is about learning the warning signs and responding to them. Continue reading “The Security Solution – Part 2”
The Security Solution – Part 1
Last week I suggested a “solution” to the problem of bad things happening in the cyber world. We want to avoid bad things from happening when we go online or when we use our computers (or phones, tablets, etc.).
I have repeatedly said you can’t prevent bad things from happening. But that doesn’t mean we are defenseless. The “solution” that I talked about last week is a blueprint for what we CAN do. This isn’t a method we are taught when we learn security. So, you won’t find it in a textbook. But it is a way of looking at the problem that summarizes a lot of the learning and experience from a formal program and translates it into a way of applying it. Continue reading “The Security Solution – Part 1”
Airport Shooting & Safety Online
Again last week, a gunman opened fire upon a crowd of people, this time in an airport. You probably heard about it. He had flown in from Alaska. He had checked his luggage, which had a gun in it. Upon retrieving his luggage, he removed the gun and began firing. Several people died, more more wounded.

I was a bit surprised that he could have done this because I didn’t realize that it was possible to ship guns in luggage that you could retrieve upon landing. I then wondered if the powers that be would now pass regulations that forbid the transport of weapons in any luggage. But then, even if they were to do that, there are other kinds of weapons such a person could use, and someone could also cause harm without any weapons.
Later, I realized that, since the baggage area is outside the security zone, this could happen another way. Anybody could drive up to the drop-off or pick-up area with a weapon, enter the building, and begin shooting. That could take place outside, in the baggage or ticketing areas, or anywhere that is accessible without passing through the security screening centers.
To prevent that, one would have to have to have security at every entrance. Can you imagine everybody that arrives on airport property going through security scanning? The cost would be tremendous, the delays would be outrageous. The flow of movement would be severely restricted. Who would pay for all that? We would, of course, through taxes and/or higher ticket prices, or access fees to enter airport property.
Even that wouldn’t prevent problems. Weapons that don’t show up on security scanners would still get through. Items that are allowed, like ball-point pens would be allowed through. A pen or pencil could be a weapon, although that would be more of a close range attack and would be against one victim at a time, even if it affected many people in succession. And someone trained in combat skills (the perpetrator in this instance was trained in combat skills) could do a lot of damage without a weapon.
So, do we begin to treat airports like federal buildings? We screen for weapons at federal courthouses and at the social security office. However, we don’t do that kind of screening at pseudo-government offices like post offices. Should we?
Some might say we should. But the cost alone would be enormous, to say nothing of the negative impact upon our access to the services we need (buying stamps, mailing packages…. or flying to our destination).
What about when we go to the grocery store or the mall. Should we be required to go through a security screening post when we go to buy milk? Or gas? Or when we walk into a bookstore, or when we buy a gift for a baby shower?
Maybe we should put law enforcement on every block and screen people who are out walking their dog? That way, we would be safer! At least the 80 year-old who is trying to maintain their mobility by walking around the block can’t gun us down. Maybe we need to screen all the cars turning onto our street so they can’t execute a drive-by shooting.

Am I getting carried away?
My point is that we can’t prevent bad things like this from happening, much as we might like to. If we try to enforce safety to the maximum extent possible, we would end up in a world that few of us would want. Novels have been written about that: 1984; Brave New World; and more recently, the Divergent trilogy. Even in those novels, there were people that didn’t conform and actions were necessary to prevent their “unlawful activity.” Even if we did have such a world, there would still be incidents! But the consequences of trying to achieve that “safety” would destroy our freedom.
One thing I know is that we can’t regulate the world into a place where these kinds of incidents CANNOT happen. I’m not saying we shouldn’t do anything. But we do seem to like making rules without considering the less obvious consequences, and we often don’t like the consequences. Even then, when we do make rules, incidents still happen. They will as long as people get angry and act on that anger, as long as people are greedy, and even when people just feel threatened. We can work on learning to behave better, but even if EVERYBODY went through training programs to improve their behavior, we would still have problems.
Let’s apply this to online security. I hope I’ve made my point that we can’t prevent bad incidents from occurring in the real world. We can’t prevent bad incidents in the cyber world either.
When we hear about a virus or some other malware that is attacking computers, we think we need some reliable way to stop it.
When we hear about a hacker, we think we need to catch them and lock them up.
When we hear about a breach of personal information, we want that company held accountable.
Here’s my message: We can’t stop these things from happening.
To do so, the world we would create would be one we wouldn’t accept.
Imagine a world where:
* You can no longer post pictures online because they could contain malware or could contain “information” that should not be published
* You can no longer share videos
* Web sites are just text, like a college textbook without pictures
* Your computer no longer goes to many of the web sites you like to go to; those sites are blocked because someone could use that site to attack you. (No more CNN, no more weather, no more Facebook, Pinterest, etc.)
* Your e-mails are returned undeliverable and the e-mail from your friends doesn’t reach you (because someone else who uses the same service as your friends: hotmail, gmail, etc., broke the rules and sent bad e-mails and now that e-mail provider is blacklisted)
And the list could go on and on.
We can’t prevent the things we don’t want unless we make it impossible to do the things we do want.
Regulation won’t solve the problem. Regulation has the following results:
* The worst offenders will ignore the regulations.
* In many cases, regulations make it harder for honest people to operate. (That’s one of the reasons I don’t currently allow comments on my blog. If someone were to make a “bad” comment, to protect myself from liability I have to meet the requirements of regulations. Those regulations have financial and filing requirements, in addition to the measures that I would naturally take without any regulations.)
* Regulation can’t stop attacks and breaches. It can only provide an incentive to people to do something about them.
Most companies would love to do something about them. However, a checklist of steps to take won’t assure you won’t be attacked or have customer data stolen. A checklist can help, but attacks will still be successful and data breaches will still occur. Trying to solve the problem by rules and regulations would be like making it illegal for you to ever make a mistake about anything:
New Federal Law: “From now on, you aren’t allowed to forget things and you aren’t allowed to make mistakes. Penalites for violation: $1000 fine per occurrence; imprisonment after three strikes.”
Most people would love to stop forgetting things and making mistakes. It’s just not possible. Solving security problems is much like trying to prevent mistakes or natural disasters.
The real solution is to:
* Take appropriate measures to make it harder for those bad things to occur
* Learn the warning signs and respond to them, which might keep us out of the line of fire when they occur
* Realize that bad things will still occur despite all efforts
* Have plans of what to do if we do find ourselves in a problem situation and what to do to reduce the damage if something bad does happen (e.g., wear bulletproof vests for an active shooter scenario; have data backups in case of a ransomware attack)
We may have limited options in an active shooter situation. We have better chances of preparation for a cyber scenario.
Doing these things won’t prevent bad things from happening. What it can do is reduce the frequency of occurrences, and reduce the severity of the impact when they do occur.

Uh-oh! That wasn’t expected!
When I was a kid, there was a short period of time that I thought I wanted to be a mailman when I grew up. I followed the mailman throughout the neighborhood as he delivered mail. At one point, I thought I was going to help the homeowners and let them know the mail had arrived. So I rang the doorbell when the postman left the mail in the box. I was quickly instructed not to do that anymore!
I don’t remember exactly how long that phase lasted. Probably not very long.
In later years, I had a “job” delivering the weekly advertising supplement to a neighborhood in the community. That was hard work. They would deliver a large bundle of the advertising pamphlet, called Penny Power, to my doorstep. They also had stacks of supplemental ads and plastic bags. First, I had to put one of each of the many advertising fliers together with each Penny Power. Then, I had to fold each Penny Power and the associated flyers and place them in a plastic bag. That would take more than a couple hours. Then, I had to go to my territory and walk up to each porch and delivery a bag of advertising goodies onto each porch. Then proceed to the next house. And the next. And the next. Until I had delivered several hundred Penny Powers with the additional advertising flyers stuffed into their respective plastic bags.
That was a heavy bundle to carry, a lot of walking, a lot of time, for a little income. Let me emphasize the word “little.” There was a lot of turnover in that job. I found out why!
I don’t see too many mail carriers delivering mail to the front doors of houses on their routes these days. Perhaps it is just the communities I have lived in recently. What I typically see instead is a mailbox on the street. The mail carrier deliveries the mail from their vehicle. In some cases, all the mailboxes for a community (or apartment complex) are located in one central location and the residents have to go to that location to get their mail.
But I do remember the days of walking with the postman to each door.
Some of the houses had a very handy arrangement for the homeowner. A mailslot in their door! They didn’t have to go outside to get their mail. The mail carrier just slipped it through the slot and it fell inside the house, just inside the door! What a marvelous invention!
Usually.
But then, there are the neighborhood mischief makers. Typically, they would run up to the house, ring the doorbell, and run away. On Halloween, they might “egg” a house. What if one of them had gotten the idea of putting rotten eggs through the mailslots? Not a pleasant thought. Eww!
How would you stop that? You could lock the screen door so they can’t put the eggs through the slot anymore. But then the postal carrier couldn’t deliver your mail. If you want your mail, you need to allow the possibility that the kids can push rotten eggs into your house.
Or, you could put up a mailbox outside your door and lock your door. Now the kids can’t use your mailslot anymore. Neither can the postal carrier. Hopefully, it won’t be so much fun for the kids to put rotten eggs in your mailbox and they will stop.
But now, the marvelous invention of the mailslot is no longer of any use to you. It has become a liability. You also had the extra expense and effort of putting up a mailbox outside your house. And you now have to open the door to get your mail. Not a lot of extra effort. But, on a freezing cold day, it’s not as nice as having it dropped inside your door. And you may need to fix your hair or put on an extra layer of clothing before getting the mail. You don’t want to get caught looking too “unkempt” by a neighbor walking by as you step briefly out the front door.
Wait a minute! I thought this was supposed to be about keeping safe online!
OK, here goes…..
Our computer has a lot of “mailslots” in it.
What I am referring to as “mailslots” are useful bits of computer programming that do cool things that we like. They make it easy for us to do what we want to do. Some may automatically show us a preview of files when we hold the mouse over them, such as showing us a picture preview. Some automatically check our e-mail every 10 minutes. Others ring a bell, play a few notes, or say “You’ve got mail!” when a new e-mail arrives. Some automatically save our progress when we are typing a letter, just in case we forget to save it.
When it comes to the Internet, some of those “mailslots” display pictures. If they didn’t, every time there was a picture, we would have to:
* Tell the computer to go out and “download” the picture.
* Then we would have to open a special program that views pictures. We would need to make sure we got the correct program for the type of picture we wanted to view. (There are several different “types” of pictures that get displayed on web pages, each with a different file extension, or “format.”)
* Then, once you opened the picture-viewing program, you would need to find the picture you downloaded and open it.
* Next, if you didn’t want to keep it, you would need to open another program that lets you work with files.
* Fnally, you would need to find that picture you downloaded and delete it.
A lot of work! And you’d have to repeat that process for EACH and EVERY picture you wanted to see. Many of those pictures wouldn’t be of any interest to you, certainly not worth all that work.
But, we don’t have to do all that work. Instead, our web browser (Internet Explorer, Safari, Chrome, Firefox, etc.) automatically displays these pictures for us. This is really useful. It enhances our experience. We can enjoy surfing the web instead of getting hung up on the mechanics of how the computer is really doing all that extra work for us. Technology is great! Until it isn’t. Until someone sticks rotten eggs through our mailslots.
And therein lies the problem. If we want our mail delivered inside our house, we have to face the risk that someone might deliver rotten eggs. If we want the convenience of “easy” and of a “rich, enjoyable experience,” we have to face the possibility someone might find a way to use those “mailslots” (useful programs) to deliver unwanted material or experiences. Those “rotten eggs” could be viruses. They could steal our information. Or they could hold our computers or information hostage, for ransom. (See my recent posts on ransomware.)
If we were to make our computers so the mischief-makers CAN’T do this undesirable stuff, we would end up with a computer that doesn’t do what we want it to. But, with computers, instead of just having to open the door to get our mail, we would have to go through ALL the above steps (and some that I haven’t even mentioned) just to see whether a picture on that web page is even one we might want to see. And, to view that web page in the first place, there could be a whole lot of additional steps involved. Most people would revolt.
So, what are these “rotten eggs”? They could be any way that an attacker can utilize some desirable feature built into our computers and use them to do something we don’t want them to do.
As an example, let’s continue with the picture-viewing discussion above. In 2004, it was discovered that there was a problem with the way Windows processed pictures so that you could view them. If someone sent you a bad picture (that is, one that someone with bad intentions had created) it could crash your program or even, in some circumstances, compromise your computer. That particular issue was fixed, but only if you updated your computer with the proper security updates.
However, that isn’t the only time that Windows has had problems with displaying pictures. As recently as May 2016, Microsoft released a security bulletin revealing that there were FIVE different vulnerabilities related to displaying images that had been recently discovered. In some cases, sensitive information could be released to the attacker. In other cases, the attacker could compromise your computer. And for this to happen, all you would need to do is visit a web page that had a “bad” picture on it. That could even be a seemingly innocuous picture on a web page that is usually considered to be on a “safe” or “trusted” site.

When this happens, Microsoft (and many other vendors) usually try to fix the problems as soon as possible (though some companies don’t). In some cases, it may take awhile to fix the problem. Once they do, the “fix” needs to be applied to your computer. For Microsoft, if you have “automatic updates” turned on, this SHOULD happen automatically (although, from experience, I can tell you that these updates sometimes fail). For other companies, you may have to apply the updates yourself. And, there are problems out there that haven’t been discovered yet. What if the bad guys find them and take advantage of them before the good guys find them and fix them. It happens all the time.
What this means is, if we want to be able to see pictures on our computers, including when we visit a web page, we will be subject to the risk that our computer can be compromised.
It doesn’t stop at picures. In 2016, Microsoft issued 155 security bulletins. Some of these advised of multiple issues. Many of them were critical.
It isn’t just Microsoft. All software is potentially subject to vulnerabilities. Microsoft’s programs are so powerful and so complex, there are a lot of pieces of programming code in which unexpected and unforeseen issues can be found. And Microsoft is a popular program, so the bad guys go looking for problems to take advantage of. (There are also a lot of good guys looking for the problems, so they can be fixed before the bad guys find them. That’s another reason so many security bulletins are issued.)
Other companies may have fewer issues. Some of that is because they are “smaller” and less “complex.” Some of that is because they are not as popular. But some of that is because they are not responding to issues and fixing them, or telling us about them.
ALL software has the potential to have these kinds of issues. (Mac and Linux users included. Yes, these systems have their issues as well, despite some people’s claims to the contrary.)
So, where does that leave us? Do we choose to lock the door so the mischief-makers can’t put rotten eggs in our mailslots? When it comes to computers, that would mean turning our computer off and leaving it off. There isn’t a way to escape these risks if we use our computers.
There are two things we can do.
First, we can keep informed of what the risks are and how to take appropriate measures to REDUCE those risks (we can’t eliminate them completely).
Secondly, we need to recognize there is still the possiblility that we can be affected by the threats. Our best response to that is to take other measures to protect ourselves against the damage that could be caused if a threat does affect us. (This would be like installing a sprinkler system to put out a fire. Damage is still done, both by the fire and by the water from the sprinklers, but not as much damage as if there were no sprinkler system to put out the fire.)
My blog is a start towards taking those two steps. This year, I will be providing additional options to go further with those steps. Stay tuned.
In the meantime, if you recognize that there is always risk, first be thankful that we have as few problems as we do. Then, use your computer with the knowledge that 100% safety is not an option and that it is up to you to do the best you can to escape as many of the potential problems as possible. Again, that comes down to learning what you can do (and then acting on that knowledge).
Your phone or tablet
So, you got a new phone or tablet for Christmas. Now, you want to install some apps. If you have an iPhone, and are going to the Apple store, you are probably in good shape.
But sometimes, people want to install other apps. Or they just feel their phone or tablet doesn’t let them do what they want to do. Maybe the app they want isn’t “authorized” or won’t install. Or maybe they want to “customize” their device, but it won’t let them.
At that point, some people turn to “jailbreaking” (or “rooting”) their phone or tablet. That is a way to disable the restrictions that keep them from installing certain apps or customizing their device.

Before you do that, there are some things you should know.
Having the phone in a “jailed” state means it is locked down for protection. It’s not so much a matter of restricting the phone as it is of protecting it. Think of “protective custody” with a lot of freedom within the bounds of that protection.
The reason the phone or tablet is “locked down” is to protect it from being affected by malicious or poorly-designed applications or activity. Another reason this is done is to prevent consumers from violating copyright laws through playing of movies or other media without proper licensing.
If one removes those restrictions, they open themselves up to a number of undesirable possibilities. That doesn’t mean they WILL be affected, but it does mean they are no longer as well protected against the possibility.
Some of the undesirable results of jailbreaking (rooting) your phone or tablet:
* Security is weakened. Malicious software could affect the phone or could steal or use your information in some other way. Malicious software may be something that gets installed without your knowledge. Or it could be an app you intentionally install that has a hidden agenda (e.g., a new game or other new app you want but that also steals your data or does other things behind your back). You would be upset about it, if you knew what it was doing.
* An app that you install may not be well-designed and may cause your device to become unstable and/or not work properly.
* Updates for security and/or improved operation or functionality may no longer be available. That would mean that you will no longer get those updates unless you install them yourself. Normally, these updates would protect you against new and dangerous threats as they become known. They may also fix performance issues and bugs as they are discovered.
* Your warranty may be voided.
* In some cases, the phone’s performance may be impacted, including draining your batteries.
* Some apps that you might install may use your data plan and use up your monthly allotment.
Apple’s app store is far less likely to contain an app that will cause your phone problems or that will be malicious. Although they may approve something they shouldn’t, your chances of getting a bad or malicious app increase considerably if you jailbreak your device and go elsewhere to get apps.
Should you jailbreak your phone or tablet?
I’m not going to say you shouldn’t. There may be a reason that you may choose to.
Just be aware that, if you choose to do so, you are making it more vulnerable. If you do so, you should be more careful about how you use that device in the future. It would be prudent not to use it for sensitive information or transactions. It would be wise to think of it from that point forward as an “insecure” device.
E-mail from my Sister!
Thanksgiving morning. Early. I check my e-mail and see a message from my sister.
3:24 a.m….. She was up early. Or maybe was still up from Wednesday night.
She said “hi phil” and then included a link, closing with her name in the format doejane (although it had her real name instead of doejane).
I looked at the link and it appeared to go to some blog.
Why is she just sending me a link?

I am always suspicious when I receive an e-mail with just a link, especially if the link looks to me like it is a blog. And yet, it appears to be from my sister on Thanksgiving day. Could it really be legitimate?
It was sent to my e-mail address that I only give to my family and a couple of other restricted places. So, if it isn’t my sister, how did they know I have this particular e-mail address.
If this were to happen to you, what would you do?
As for me, I wouldn’t follow the link. If it isn’t a safe link, clicking on it is a good way to get your computer compromised . Even if the e-mail is really from someone you know. I looked a little further.
The e-mail address was [mysistersname]@tampabay.rr.com. Well, that’s strange. If it ends in tampabay.rr.com, that means that the person sending it gets their Internet service from Charter Communications, previously Time Warner Cable. More specifically, they get it from the TampaBay location for that provider. That means they are/were located in the Tampa area. (Or they are faking their address as coming from there.)
But my sister lives in the northeast part of the nation.
Strange.
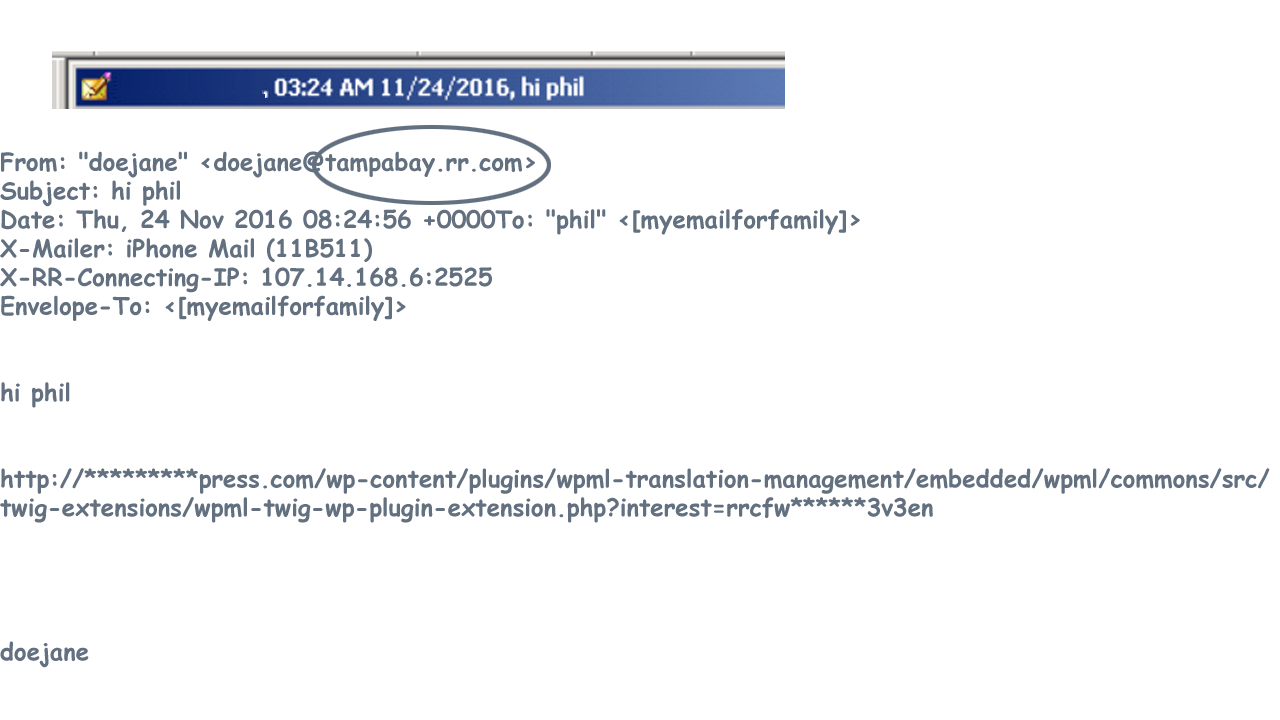
So, now I have the following information:
The person sending the e-mail connects from a Tampa area account (or pretends to).
The person’s e-mail sounds like a personal e-mail but only includes “hi phil” plus a link, and then their name (run together with no space, last name first).
This is pretty suspicious. It has to be an attempt to fool me. If I were to click on that link, I would likely have a compromised computer.
But the perpetrator did several things amazingly well.
1) They used my sister’s actual name. It is a bit unusual that it is lower case and signed “last name first,” run together with no space. But some of my friends sign their names all lower case.
2) They sent it to me using my e-mail address that is given out to very few people. I give out my other e-mail addresses to lots of people, but not this one.
3) They sent it on Thanksgiving Day, a time that loved ones are more likely to be in contact with us.
Would you have clicked on the link?
So, how should you handle this? The bad guys are smart (at least some of them). You don’t want to ignore e-mail from loved ones.
Let’s examine this situation. There are clues that there might be a problem.
The biggest clue is the address specifies it came from the wrong part of the country. But if the address had been from @gmail.com, we wouldn’t have that clue. And, even for me, I didn’t discover the problem with the address until I started looking, which was after I was already suspicous.
The biggest giveaway for me was that the e-mail contained only a link between the greeting and signature. This is always suspicious to me. Of course, some of my friends regularly send e-mails like that. Maybe some of your friends do as well. With those friends, at least that is their pattern for sending e-mails. But, I often don’t click on their links either.
My response to such cases is the following:
* I pay attention to the link itself. I recognized this as likely being a blog. I know that a lot of attempts by attackers use this technique. (It really helps to become familiar with the techniques attackers use so you can recognize attempts when they occur.)
* As a rule, I don’t click on links just because someone sends them. I evaluate the likelihood that it is safe and also whether I think it might actually be of interest.
* If I thought this really did come from my sister, I still wouldn’t click on the link because it looks too much like the style used by attackers. I would contact her first and make sure it really came from her (even if the e-mail address was her true e-mail address) and try to get some more information about it.
(By the way, I did receive an e-mail from my sister later that day. It didn’t have links to blogs, but had actual sentences with relevant remarks. Also, it came from her REAL e-mail address, which was in the format of janiedoe@…… instead of doejane@.)
Final analysis:
The e-mail likely came from someone who was either trying to compromise computers or someone trying to sell something. (I’m sure you’ve seen spam e-mails for weight loss, body part enhancement, pills, etc.)
Be careful when you go through your e-mail. Even if it comes from someone you know or is about something you are interested in. The bad guys will use holidays, events, or anything else to trick us into opening their e-mails.
What else are they likely to do at this time of year? You may have seen e-mails about failed delivery attempts from DHL or UPS. Do you have any packages coming at this time of year? I do.

In fact, UPS failed to deliver the package I had ordered. The tracking information said it was on the truck for delivery this past Monday, but it didn’t arrive. The next day, it was scheduled again to be delivered. A little after 3:00, I looked online and the tracking info said they had delivered it. Nobody had rung the doorbell but I looked around outside. The package wasn’t here. I had to call the shipper, and they are filling the order again.
But, what if I had gotten an e-mail from UPS? It would be tempting to open it since they had failed their delivery a couple times already. If a bad guy had sent me one of these e-mails in the last couple days, the scenario was ripe for me to open it to find out what was happening with my delivery. Knowing that this is how the bad guys operate, I still wouldn’t have opened the e-mail. I would have gone to the shipping company’s site using the tracking number I already had (which is what I did). Then, I would have called them using the number I already had (which I also did). They said there was nothing they could do since it was marked as delivered.
They didn’t send me an e-mail about this. But what if they had? Do you think I would have opened it, because of being upset about their failures and hoping for some kind of satisfaction? Suppose a bad guy had sent a malicious “failed delivery” e-mail this week. I’ve certainly received a bunch of those in the past. But this time I already knew there were delivery problems. And I wanted it fixed!
What would YOU have done? Would you have clicked to find out what was going on with the failed delivery?
The main thing I want you to take away from this is:
Think before you click.
Many of us are overloaded with information. Some of that comes through e-mail, especially if you get lots of e-mail. If we are feeling like there’s too much information coming our way, it is easy to pay less attention to individual e-mails. That could put us at risk for falling prey to at attacker’s tricks, because we fail to think before opening the e-mail or clicking on a link.
I get a couple hundred e-mails daily. Most of them are never opened. I scan through the sender names and subjects fairly quickly. Some are deleted. I place the majority into an “archive” folder without opening them. They are there if I ever need to refer back to or search for something. Only a few get opened. One of those was the e-mail from my sister. Or rather, the one that looked like it was from my sister.
It is important to keep paying attention. As we open the e-mails that we think are of interest or from someone we want to hear from, we need to be aware of the possibility that it could be a trick. It could be someone pretending to be our family or friend. Or it could be an e-mail about something that is very relevant to our life on that particular day, such as a package that we are trying to get delivered. Holidays are a time that some of the bad guys step up their attacks. It is also a time that we may be more susceptible.
Think before you open or click.
The second thing is to become aware of the tricks the bad guys play so you don’t fall victim to them.